Evidence gathering and chain custody. A key consideration in any investigation must always be how to secure or preserve sufficient evidence to prove a case of fraud. It is vitally important that control is taken of any physical evidence before the opportunity arises for it to be removed or destroyed by the suspect.
Therefore, physical evidence may need to be seized at an early stage in the investigation before any witness statements are collected or interviews conducted. If a criminal act is suspected, the police should also be consulted early in the process before any overt action is taken and the suspect is alerted.
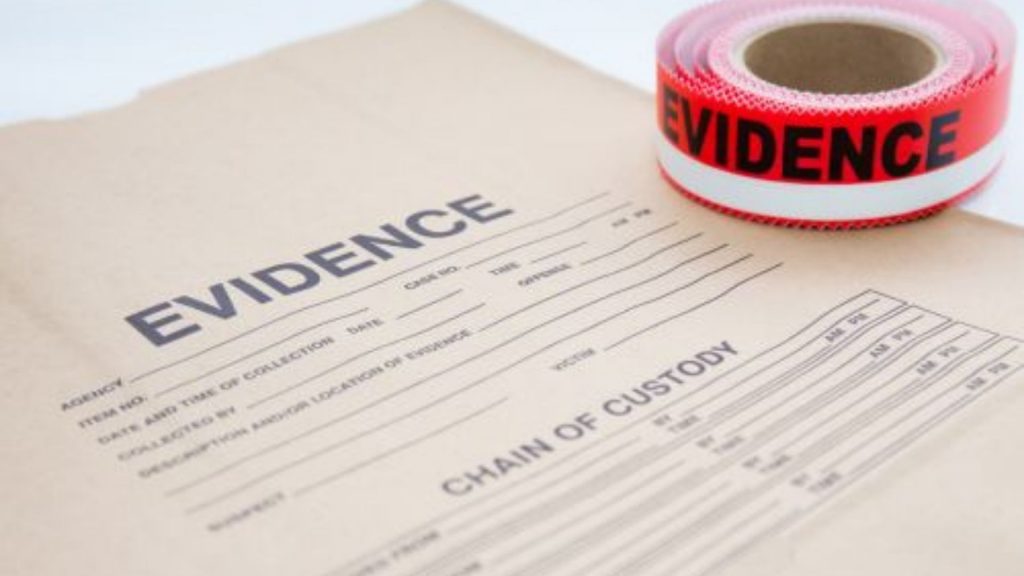
Evidence Gathering And Chain Custody
If an individual does end up being charged with a criminal offense, and this may not be planned at the outset of the investigation, all investigations, and relevant evidence arising from such investigations, will be open to discovery by that individual’s defense. It is, therefore, important that proper records are kept from the outset, including accurate notes of when, where, and from whom the evidence was obtained and by whom.
The police, or legal advisers, will be able to advise on how this should be done. If appropriate, written consent should be obtained from the relevant department or branch manager before removing any items. This can be done with senior management authority, as the items are the organization’s property. Similarly, electronic evidence must be secured before it can be tampered with by the suspect.
Chain Of Custody
The concept of the chain of custody refers to the logical sequence of gathering evidence, whether physical or electronic, in legal cases. Each link in the chain is essential as the evidence presented for consideration in a civil or criminal legal case may be rendered inadmissible. In this way, preserving the chain of custody is about following the correct procedure and making sure the quality of evidence brought before the courts is top-notch.
The everyday use of digital evidence in legal cases now means that the chain of custody must be captured and maintained when collecting and handling electronic evidence. For any given case, the chain should be documented to show the end of the sequence of work undertaken, including by whom, when (i.e., date/time), and the purpose.
Furthermore, the chain of custody is not just a requirement of the Courts, but it also supports the evidence examination process by ensuring data elements are not just scrutinized from a single dimension. It encourages each item of evidence to be considered from the perspective of where it came from (i.e., company, device, geography), who created it, when, and why.
This means that by viewing the whole chain of custody, evidence that may otherwise seem unhelpful to an investigation may serve as being useful.
What Is The Process Of A Chain Of Custody For Digital Evidence?
To protect digital evidence, the chain of custody should span from the first point of data collection through examination, analysis, reporting, and the time of presentation to the Courts. This is important to avoid the possibility of any suggestion that the evidence has been compromised in any way. While it may have been handled correctly during the process, if the evidence is then handed to the Court to leave it open to alteration, perhaps by changing the timestamps or metadata associated, it may then be damaged.
Data collection
The chain of custody begins from the first item of data collected. The examiner must ‘tag’ each item acquired and document the source, how and when it was collected, where it is stored, and who has access.
Examination
The chain of custody must be documented during the examination process, outlining the process undertaken. It is useful to capture screenshots to show the tasks completed and the evidence exposed throughout the process.
Analysis
It may be appropriate to capture the chain of custody information during the analysis stage.
Reporting
At the reporting stage, the chain of custody is documented in a statement that explains the tools used, the sources of data, methods of extraction used, the process of analysis, issues encountered, and how these were controlled. Ultimately, this statement must make it clear that the chain of custody has been maintained throughout the process and that the evidence given is legally defensible.
To maintain the chain of custody, digital experts are well-practiced in using contemporaneous note-taking, allowing them to document the processes undertaken and recreate the results they have achieved.
How Can The Chain Of Custody Be Assured?
In addition to taking contemporaneous notes, digital examiners use some of the best practices to preserve the chain of custody, including:
Examining the scene before data is taken can damage a case if an examiner acts too rapidly in identifying and capturing data and devices of interest without assessing the situation and ensuring the scene is secure. This includes making sure that removing an item will have no negative impact on ongoing IT service provision, documenting the wider context and existing infrastructure from which the data item is being taken (including number and type of computers, network type, details of key administrative personnel, types of software used and operating systems used) – this may provide useful information which is material to the investigation.
Using copies of the data captured – the central part of preserving the original evidence cannot be overstated, as if damaged or compromised in any way, the case may be jeopardized. There are many ways by which copies of digital evidence can be made and then used for examination and analysis, including creating a ‘bit-for-bit (i.e., digitally identical) clone of individual data items or whole system contents.
Ensuring the storage medium is sterilized – if an item of data is placed on to an examiner’s storage device (i.e., hard drive), that medium must be entirely clean and free of any possible contamination at every level.
The digital chain of custody is the center of every action taken by digital specialists. They understand that days or weeks of intensive work would be wasted if they miss a step in the process or fail to ensure the integrity of the evidence they have worked so hard to find, analyze, and document. Hence, integrity is always first in the minds of digital examiners.
Final Thoughts
A prosecutor must prove that the evidence presented in court is the same evidence that was recovered at the scene of an alleged crime in order to convict someone. They must be able to demonstrate that the evidence was properly handled and was not contaminated or tampered with. If law enforcement fails to handle evidence properly, it can be challenged on the grounds that it was tampered with, that test results are faulty or inaccurate, or that evidence was planted at the scene of a crime.